Securely Use Cloud Storage Services
Everyone is responsible for minimizing the risk of data loss or exposure for files stored in cloud storage services. Learn how to protect Cornell’s data from unauthorized access.
This article applies to: Box , Cloudification , Cornell Google Workspace for Faculty and Staff , File Storage at Cornell , OneDrive , Security & Policy , SharePoint
General Guidelines
The online file services from Box, Google, and Microsoft are only approved for moderate-risk data. Do not use these cloud services to store Personally Identifiable Information (PII) or other high-risk data. See the Regulated Data page for more information.
Cloud Storage Options
Use a Cornell-approved, cloud-based file service to securely store and collaborate on low and moderate-risk data types. These include:
- Box
- Microsoft 365 (OneDrive, SharePoint, and Teams)
- Google Shared Drive (Note: Do not share from Google My Drive because of significant ownership issues.)
Use Your Cornell Login Credentials
Sign in using your Cornell NetID (NetID@cornell.edu) for the Cornell-contracted service; do not use a personally purchased account. Cornell vendor contract language that legally covers Cornell’s services does not apply to personal accounts.
Cornell services are configured to be as secure as possible and provide a complete directory of Cornell employees for applying permissions and sending notifications.
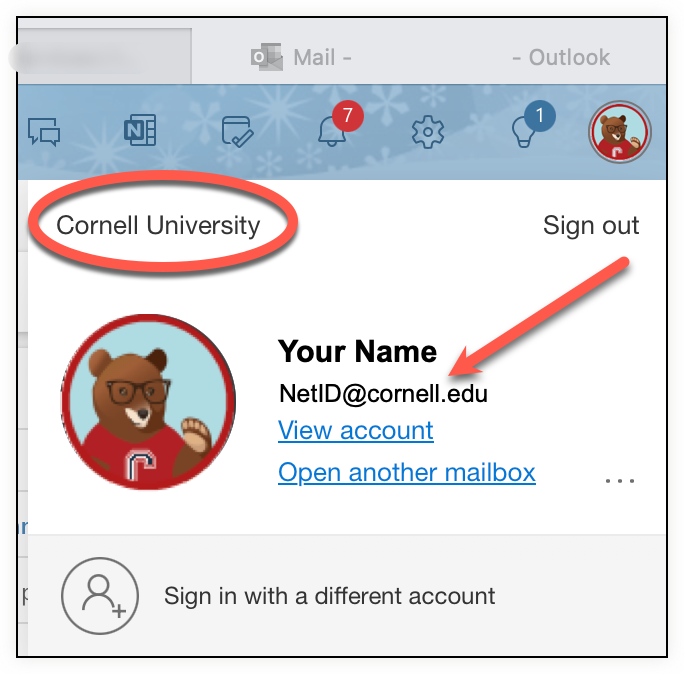
Microsoft 365 on the Web
To check your Microsoft 365 account, look for the personal logo at the top right of the browser window. It may display a personal icon (if you set that up) or your initials. Click on that icon:
Review the information on the box that appears. Look for Cornell University as well as your NetID@cornell.edu.
Box and Google
The Cornell Logo will be displayed in the banner at the top of the page.
A Cornell Box Account
A Cornell Google Account
Create Shared Folders
When collaborating on files, it is good practice to create a shared, well-structured group file space that is separate from your personal file space. This ensures that more than one person knows where essential files are after you move on from your position, and that the shared files do not use your personal drive storage quotas.
| Service | Available Shared Space |
|---|---|
| Box | Box Departmental Folders |
| Google Shared Drive | |
| Microsoft | Teams or SharePoint |
Recommendations for Shared Folders
Set Permissions Carefully
When you share a resource (file or folder) use explicit permissions. This means give specific people access at a specific level, such as edit or view only. All the file services are set up with restricted sharing by default.
In addition:
- Provide access to sensitive data only if needed to fulfill professional responsibilities.
- Give at least one other person administrative-level access so they can manage permissions if you are unavailable or leave your position.
- Ensure your unit or organization has a process to review and remove access to sensitive data when people leave, and for those who no longer need access (such as a role change.)
Check Permissions When You Reorganize Folders
If you move or copy a folder into an existing shared folder (the parent), it will inherit the parent folder’s permissions. This means its contents will be available to everyone who can access the parent folder.
Restrict Sharing
You can restrict collaborators’ ability to further share folders or files to prevent inappropriate distribution. These capabilities vary by service.
| Service | Capability |
|---|---|
| Box |
|
| Google Shared Drive |
See Limiting Sharing. |
| Microsoft |
See Manage Access Requests (SharePoint). |
Label Sensitive Content
Apply labels to remind collaborators that they should be careful about sharing access to a specific file.
| Service | Capability |
|---|---|
| Box | Apply tags to indicate that content is sensitive. |
| Google Shared Drive | Apply labels (requires a Plus license) to sensitive content. |
| Microsoft | Apply labels (requires A5 license) to sensitive content. |
Using Links to Share Information
The cloud services offered at Cornell make it easy to share a resource using a URL or hyperlink. Keep in mind the following:
- When sharing a link, do not use “All of Cornell” or “Anyone with a Link” (available in Google Drive and Box). Even if you send that link to a specific email address or group, there is nothing to prevent it from being shared beyond what is intended.
- The best practice is to apply specific permissions for the individuals involved to the folder, files, or other resources and then send the link to those with access.
Synchronizing for Offline Work
All the file services allow files, folders, or entire file libraries to be synchronized (mirrored) between the cloud file service and a personal device. This allows you, and other collaborators, to work on files locally, then merge changes with the online file. This is particularly helpful if you expect to have no, or poor, internet access, or are working with a large file, especially with many images.
| Storage Choice | Box Drive | Google Drive | Microsoft OneDrive |
|---|---|---|---|
| Store files in an online (cloud) location and stream them on demand to your computer. | yes | yes | yes |
| Store a copy of an online file locally for offline access. | Choose specific folders for offline. | Mirror everything or choose specific folders. | Mirror everything or choose specific folders. |
Minimum Device Security
If you synchronize files containing sensitive data, it must be stored on:
- A Cornell Certified Desktop Device
- Certified Desktop provides cybersecurity software and configuration to secure your device.
- Check your Certified Desktop security status using the Cornell Certified Desktop Self-Check App.
- Encrypted Tablet or Smartphone
- A fully encrypted smartphone used only by you that is never shared (say, with a family member).
- If your smartphone is protected by any authentication method (PIN, Password, Fingerprint, or Face) for any device running IOS 7 (2014) or Android 6 Marshmallow (2015) or later, then it is automatically encrypted.
- For more information, refer to Mobile Devices in Policy 5.10, Information Security.
Limit Synchronized Files
The fewer places sensitive data is kept, the less likely it is to result in unauthorized disclosure. Details for configuring synchronization are available for Box, Microsoft OneDrive, and Google Drive.
- Select Specific Folders
- You can mark the specific folders you need to access from your device. The contents of these folders will then be displayed in the file manager features of your device.
- One way to simplify the secure management of your work is to create a single folder for synchronizing sensitive data (name it something obvious like “Sensitive Data on My Device”).
- Use the online web file management interface to move folders or files you need on your device into and out of this folder as needed; this makes it easier to see and manage the sensitive data on your device.
- On-Demand or Offline Synchronization
- You can specify whether folders should synchronize to your device immediately or if they should download to your device when you first open them.
- If you expect no or poor internet access, configure your synchronization service to make files available offline.
Data Retention
Data must not be retained beyond the retention period defined in Data Retention Policy 4.7.
Cornell Secure File Transfer
Although Cornell Secure File Transfer is not suitable for active collaboration, it is good for occasional transfers.



Comments?
To share feedback about this page or request support, log in with your NetID