Scan for Confidential Data: Windows
Spirion scans your computer for confidential data.
This article applies to: Spirion (formerly Identity Finder)
Spirion is a tool to help you locate confidential data on your machine, but you’ll need to work through the results before you can be sure your machine is in compliance with University policy and local practices. Spirion is configured to run automatically, but you can also perform manually-triggered scans.
General Process
- The copy of Spirion you install has been configured by Cornell to scan specific areas of your machine and to look for particular data types. Cornell classifies as confidential any of the following (when they appear in conjunction with an individual’s name or other identifier):
- Social Security numbers
- Credit card numbers
- Driver’s license numbers
- Bank account numbers
- Protected health information, as defined by HIPAA (Data scanning tools cannot identify this type of data. You’ll need to search for it separately.)
- Spirion produces a list of possible matches.
- Next check each match and decide how to handle it securely. For more information, see How to Handle Scan Results.
At a minimum, you should scan your entire computer and any attached drives. If you are searching removable drives, you’ll need to do a second scan. See Scan for Confidential Data on External Drives: Windows. (Always check with your technical support provider to find out what local practices should be followed.)
Important! If you use Outlook on the Web consistently to read email, you need to download your email to your computer before scanning. Spirion can’t scan email stored on the Office365 server. Configure Outlook to download your email to scan your mail files.
Scan for Confidential Data
Warning: Departmental practice may differ from the procedures given here. These are general instructions for running Spirion at Cornell. Some departments and units are delivering pre-configured copies of the software, and different groups will take different approaches to handling confidential data. This means that some of the procedures given here may not be relevant for you. Always follow local practices and guidelines when scanning and making decisions about data.
It is a good idea to back up your machine before scanning. If you shred data accidentally, you can recover it from the back up.
- From the Start menu, select . If this is the first time you’ve used Spirion, continue with Step 2. Otherwise, skip to step 3. If your computer has multiple profiles, you must run Spirion with elevated (admin) privileges in order to scan all of the profiles. Right-click Spirion and click . Type the administrator password, and then click .
- In the New Spirion Profile window, enter a password, confirm the password, and then click . In the Profile Password box, click . Note: Do not use your NetID password.
- If prompted, in the Spirion Profile Sign In window, enter your password, and then click .
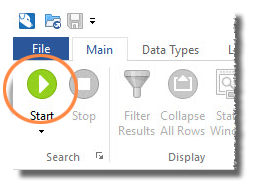
Click , and then click .
By default, Spirion searches your whole computer (including locally-stored mail) for Social Security numbers, Credit Card numbers, Bank Account numbers, and Drivers License numbers. If you want to change where it searches and what it searches for, click the small arrow below the Start icon, then select Start Search Wizard. Spirion begins scanning. You’ll see a Status window where you can track the scan progress.- When the scan is complete, Spirion displays a list of files containing confidential data. If you want to save the results file (this is optional),
- Click , then choose a location and file name.
- Enter a password to use for the scan results file, confirm the password, and then click . Note: Do not use your Identity Finder profile password or your NetID password for the results file.
- If you wish to review the results, click .
- Review the list of files identified by the scan. You must look at each file and decide how to deal with it. Always follow local practices to determine the best way to handle files identified by the scan. For more information, see How to Handle Scan Results.
- When you have dealt with all the files in the list, quit Spirion.

Comments?
To share feedback about this page or request support, log in with your NetID