Latest News

When critical systems fail at scale, the immediate impact is impossible to miss: grounded flights, stalled operations, and students suddenly unable to access assignments, submit coursework, or complete exams. But the outage isn’t the only problem.
What follows—often within hours—is a quieter, more personal threat: a surge of emails, texts, and messages that appear to offer help, restore access, or provide urgent updates, but are actually designed to steal information. Resist the urge to respond to messages promising quick fixes or restored access.
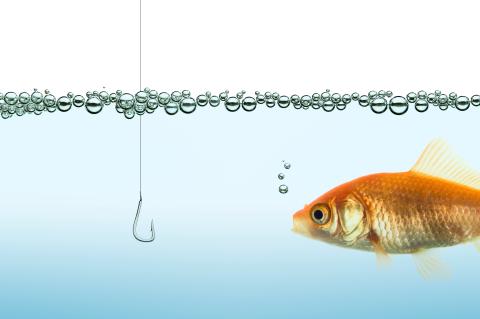
Bad Actors Treat Chaos as Opportunity
What makes these scams so effective is timing.
In the hours after a major outage, the risk of phishing doesn’t just increase—it spikes. Cybercriminals move quickly, using the same news and confusion everyone else is seeing to craft messages that feel timely and legitimate. At the very moment people are checking for updates or trying to regain access, attackers are sending emails that appear to offer exactly that.
The potential reach of those attacks expands in the confusion that follows. When a widely used system is affected, it gives scammers a recognizable name to impersonate and a shared context they can exploit. Messages referencing outages, account access, or urgent updates can be sent at scale—and still feel personal.
That combination of urgency, familiarity, and scale creates a particularly risky moment. Even when systems themselves are secure, the focus shifts to individuals—who may be more likely to click a link, respond to a message, or trust a request that promises an easy solution.
Don’t fall for the offer of a quick fix.
Remain Skeptical and Follow Trusted Sources
That’s why, in addition to updates about restoring service, organizations often issue a second type of message: a warning to stay alert for scams tied to the incident.
These alerts are designed to do more than raise awareness. They help re-establish what’s trustworthy, reminding people to rely only on official channels—not unsolicited emails, texts, or links.
They also encourage people to slow down and verify before taking action, countering the urgency that scammers depend on. And they spell out what to watch for: messages about password resets, account recovery, or “support” outreach that may not be what they seem.
Clear, timely communication helps close the gap attackers try to exploit. When people know what to expect—and what to question—they’re far less likely to fall for it.
Report Suspicious Messages
Identifying suspicious messages doesn’t just protect you—it helps protect the entire community. Reporting helps security teams detect patterns, block similar attacks, and reduce risk for others.
Use the built-in reporting tools in Microsoft Outlook and Gmail to flag suspicious emails.
Quarterly phishing simulations also help build awareness, making it easier to recognize and report real threats when they appear.
When Systems Go Down, Stay on Guard
In the aftermath of an outage, not every message is what it seems. The same disruption that interrupts work, travel, or learning also creates an opening for exploitation.
The best defense is simple but powerful: pause, verify, and trust only confirmed sources.
When systems go down, awareness—not speed—is what keeps you secure.

Comments?
To share feedback about this page or request support, log in with your NetID